Disney Galaxys Edge
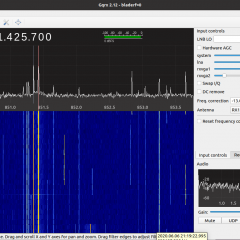
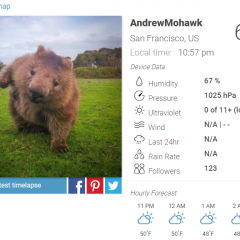
TL;DR — Disney star wars games involve a bunch of scanning Aztec codes for items and challenges, I couldn’t figure out how to generate my own correctly so I took apart the APK and generated each one I found with its description and put all the barcodes on my GitHub page for this. Recently, my…