Overview
I’ve always been semi interested in botnets/trojans and targetted attacks and the way they get their data in and out and how the command and control centres work. One of the things i’d usually do is see if I can determine where the traffic is going from the bot (infected machine) and this would obviously point me to the c&c. I’d then fire up Maltego and start playing with that IP/hostname to see where else it appears, what other things are linked to it and so on. One of the concepts I was playing around with was how could you hide where your c&c and from this FireBridges as a concept where created.
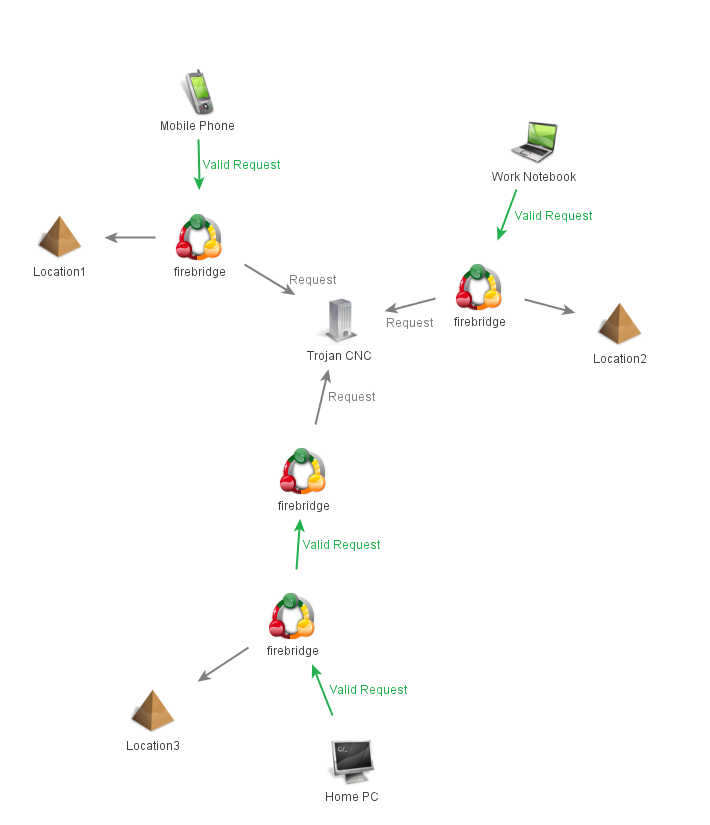
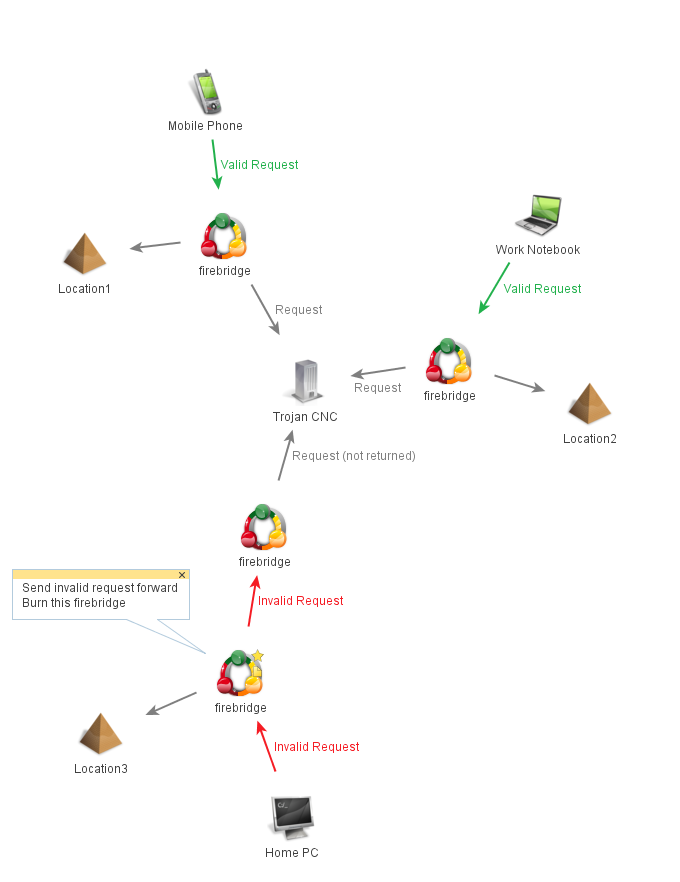
Since we were playing badguy-badguy I decided to think how do the good guys go about taking apart a bot to get to your c&c and i figure it probably works something like this:
* What is c&c.thisisnotnormal.traffic.com – browse to it, portscan, etc
* Look at traffic going to c&c.thisisnotnormal.traffic.com – replay it to see results
* Take apart the traffic and start sending modifying parts to see results
* Go and literally pick up the machine(s) hosting c&c.thisisnotnormal.traffic.com
So how would you go about making these peoples lives a little more painful?
* Make sure no connections go directly to the c&c – route through proxies
* Make sure all traffic is encrypted/encoded and if either fails destroy the proxy
* All proxies look for replay attacks and destroy themselves after a threshhold (could be 1 for the super paranoid)
Basics
From this the idea of Firebridges (really thought it was a cool name but i see there are loads of other things with the same name) were born. The idea is relatively basic:
* You have a series of proxies that dont know about anything apart from the nextHop in the chain
* Proxies all make sure that data passing through is correctly encrypted (checking for tampering)
* Proxies all make sure data is not being replayed
* If a proxy detects something going wrong it removes all files associated with the nextHop leaving the people chasing you with a dead end
Implementation was not too difficult, whipped something up in PHP that works like this:
* All requests to nextHop include a POST variable ‘key’ that contains a key made up of the following (B64(RIJNDAEL256(B64(secretkey))):
1. b64_1 = Base64_encode(‘text’)
2. RIJ_2 = RIJNDAEL_256_encode(b64_1)
3. b64_3 = Base64_encode(RIJ_2)
* All requests hit a ‘bridge.php’ page that does:
* @Include ‘proxy.php’, call function proxyRequest(); which checks auth above and replay attacks via SQLite db
* If proxyRequest() returns false, remove the SQLite database and ‘proxy.php’ script leaving the person chasing you with a 5 line php file that once included something
* If proxyRequest() returns != false, simply return the page to the browser.
Results
Using FireBridges, you can now create a proxy network easily by simply changing the nextHop variable in proxyRequest.php and adding them to machines all over the world that will burn if anyone tampers with them. This means if anyone is investigating why traffic is going to thisisauniquehostname.weareevil.com and decides to browse to it the proxies will burn themselves (and they will get the default apache page – configurable in bridge.php) and by the time they pick up the machine all they will have is 1 php script that gives away nothing. It also means that if these investigators are slightly more resourceful in their approach and try replay the attack after a certain threshold of replays (default is 2) the next replay will burn the proxy. Finally if they are even more resourceful and try tamper with any of the data the proxy will burn on the first attempt presuming it doesn’t match your requirements.
Defenses
So defending against this is pretty tricky but essentially it comes down to the following:
* Always assume a replay threshold of 1 if you see anything like this
* If you spot a c&c then DO NOT TOUCH it networkly prior to making a full image of the machine
* If you are unsure about where the c&c is but can see the traffic, keep monitoring it but do not touch the bridge before picking it up, remember one bad packet could burn the entire route to the c&c
Code
So onto the code (I realise this format sucks, but there are download links for each script below each heading):
firebridge.sqlite (db for checking replays)
sqlite> .tables seenKeys sqlite> .schema CREATE TABLE seenKeys(KEY text, COUNT SMALLINT); |
exampleRequest.php (script to request something via fireBridge – used in bot?)
bridge.php (script initially called)
proxyRequest.php (actual proxy)
-AM
Hi Andrew,
I am new to Maltego, i was searching for some transforms and as i was reading through some of the blogs and websites and ended up reading this blog of yours,could y ou please help me out in how to integrate firebridge with Maltego
regards,
Rajesh
Hi,
I’d recommend you re-read this entry, Maltego was only used here to demonstrate what a firebridge is and where you can use it rather than an integration into Maltego.
-AM